S3 Access Logs Not Working
Ideally, this s3 bucket will have been configured to not allow any deletes and should be in a separate aws account. However, should you have a requirement to understand who is accessing your s3 buckets, then this logging can quickly and easily be enabled.

Server Access Logging In S3 Cloudaffaire
With lambda service logs and cloud watch service enabled by default.

S3 access logs not working. Configure aws services for the generic s3 input. Make sure you have installed aws client on your system if not you can follow the following link to install Check the target bucket's access control list (acl) to verify if the log delivery group has write access.
To enable remote logging in airflow, we need to make use of an airflow plugin which can be installed as a part of airflow pip install command. Hi, i am facing an issue where event is not being created and associated with lambda, although it is specified in sam: This is great for archives like logs you already processed but might want to look at later.
This can be performed by disabling bucket access logging, and reenabling it per the documentation above. With web sync worker i can read logs already in s3 (i just added some dummy files for testing) but workers are not writing any new logs into the s3 bucket. You do not need to change the remote_log_conn_id because we have exported our s3 connection in airflow_conn_s3_uri task_log_reader = s3.task logging_config_class = log_config.logging_config.
Follow these steps to check and modify the target bucket's acl using the amazon s3 console: Please refer to this blog entry for more details. Can you please make sure you are connecting to the same s3 region as your bucket:
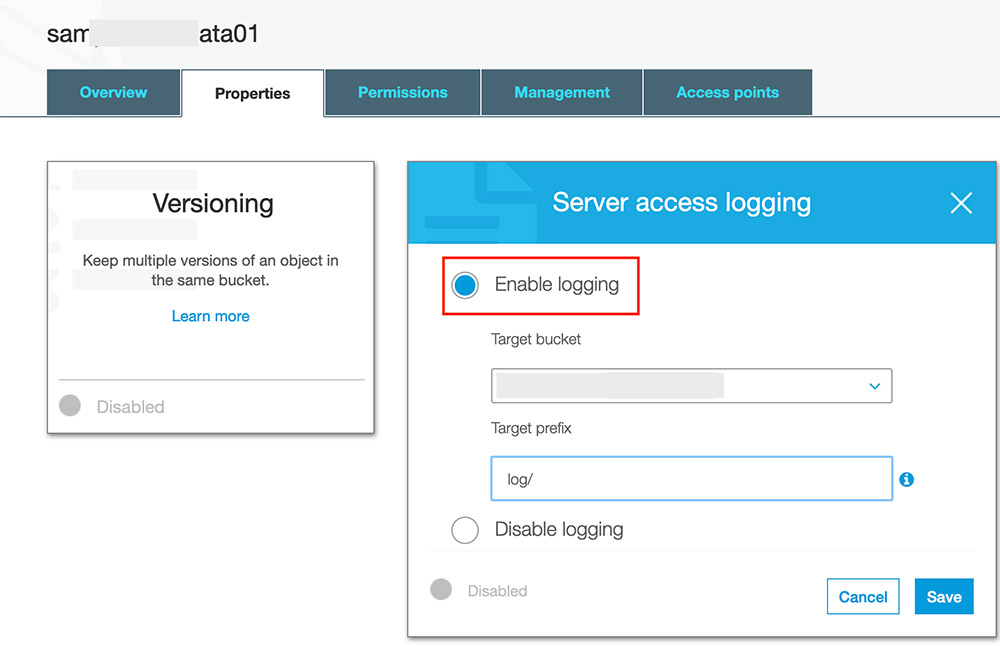
Verify that logs are showing up for newly executed tasks in the bucket you’ve defined. Amazon s3 block public access can apply to individual buckets or aws accounts. To collect access logs, configure logging in the aws console to collect the logs in a dedicated s3 bucket.
First, create a new bucket in which to save the s3 access logs. One side note though, you don't have to disable static website hosting. See the aws documentation for more information on how to configure access logs:
Simply removing the bucket policy which allows public access is enough. After upgrade, we realized that below feature is not working, which was working in v1.53.3. Retrieve the aws iam user for your snowflake account.
Create a cloud storage integration in snowflake. Glacier gives you much cheaper storage with much slower and more expensive access. Create the iam role in aws.
Configure access permissions for the s3 bucket. The permission should now be visible on the destination bucket and logging should continue. If older logs are loaded into the s3 bucket or the only_logs_after option date is set to a date/time earlier than previous executions of the module, the older log files will be ignored and not ingested.
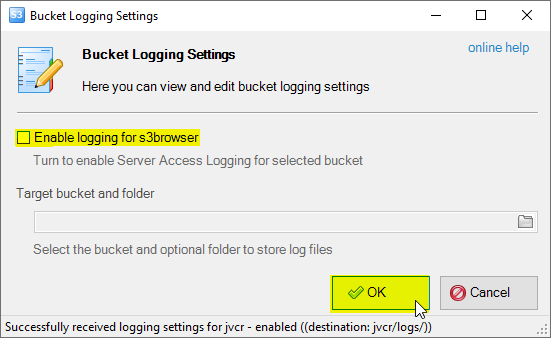
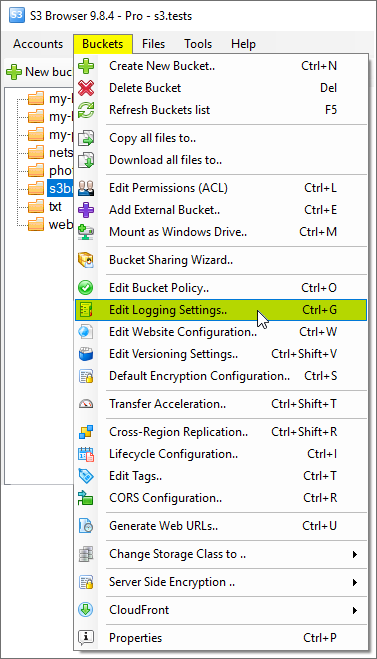
Open the amazon s3 console. From the list of buckets, choose the target bucket that server access logs are supposed to be sent to. In the buckets list, choose the name of the bucket that you want.
You can't enable s3 object lock on the target bucket. By default, when you create a new bucket, access logging is not enabled. If you're getting access denied errors on public read requests that are allowed, check the bucket's amazon s3 block public access settings.
Review the s3 block public access settings at both the account and bucket level. Task_log_reader = s3.task logging_config_class = log_config.logging_config remote_log_conn_id = s3</strong> platform hook>. Restart the airflow webserver and scheduler, and trigger (or wait for) a new task execution.
The configuration of this process is based upon a source bucket and a target bucket. These settings can override permissions that allow public read access. Can confirm, same issue with airflow2.0.0rc1 on kubernetes 1.16 on eks.
Grant the iam user permissions to access bucket objects
Aws S3 Logjam Server Access Logging Vs Object-level Logging - Netskope
Aws S3 Logjam Server Access Logging Vs Object-level Logging - Netskope

How To Instrument S3 Access Logs For Security Monitoring Panther
Aws S3 Logjam Server Access Logging Vs Object-level Logging - Netskope

Centralized Logging Architecture Diagram Implementation Guide Data Visualization Change Management

How To Instrument S3 Access Logs For Security Monitoring Panther
Amazon S3 Bucket Logging How To Configure Server Access Logging Amazon S3 Access Logs Format Amazon S3 Logging
Amazon S3 Bucket Logging How To Configure Server Access Logging Amazon S3 Access Logs Format Amazon S3 Logging

Exporting Of Aws Cloudwatch Logs To S3 Using Automation Step Function Automation Aws Lambda

New Amazon Cloudwatch Logs Insights Fast Interactive Log Analytics Amazon Web Services Analytics Interactive Insight
Analyzing Amazon S3 Server Access Logs Using Amazon Es Aws Big Data Blog

Server Access Logging In S3 Cloudaffaire

Server Access Logging In S3 Cloudaffaire

Serving Private Content Through Cloudfront Udemy Online Courses Learn A New Skill

How To Instrument S3 Access Logs For Security Monitoring Panther

New Amazon Cloudwatch Logs Insights Fast Interactive Log Analytics Amazon Web Services Interactive Insight Analytics

Analyzing Amazon S3 Server Access Logs Using Amazon Es Aws Big Data Blog

Centralized Logging Aws Answers Aws Lambda Log In Web Server

New Amazon Cloudwatch Logs Insights Fast Interactive Log Analytics Amazon Web Services Interactive Analytics Insight